The tips in this article were provided by Brecht Ryckaert – our resident WordPress expert. The book he published on WordPress security, speaks very well about his years of experience with the popular CMS.
Click on the link to learn more about WordPress Security 101.
Regardless of whether you have your own custom coded website or you are relying on a CMS, first and foremost, you need to always follow the general rules to prevent your website from getting hacked. Those are common sense rules you need to be mindful of at any time.
In this article, you will also find anti-hacking measures you can take to protect your website, specific for WordPress:
Install a good security plugin: Wordfence
You need a good security plugin within WordPress. I myself use Wordfence for this, given that it has a very good “track record” with regard to updates, that it does not cause any leaks itself and a quick roll-out of fixes or measures against new hacking attacks and / or leaks.
In addition, you can set Wordfence very strict by configuring the following options (or so I do this anyway):
Recommended settings for Wordfence
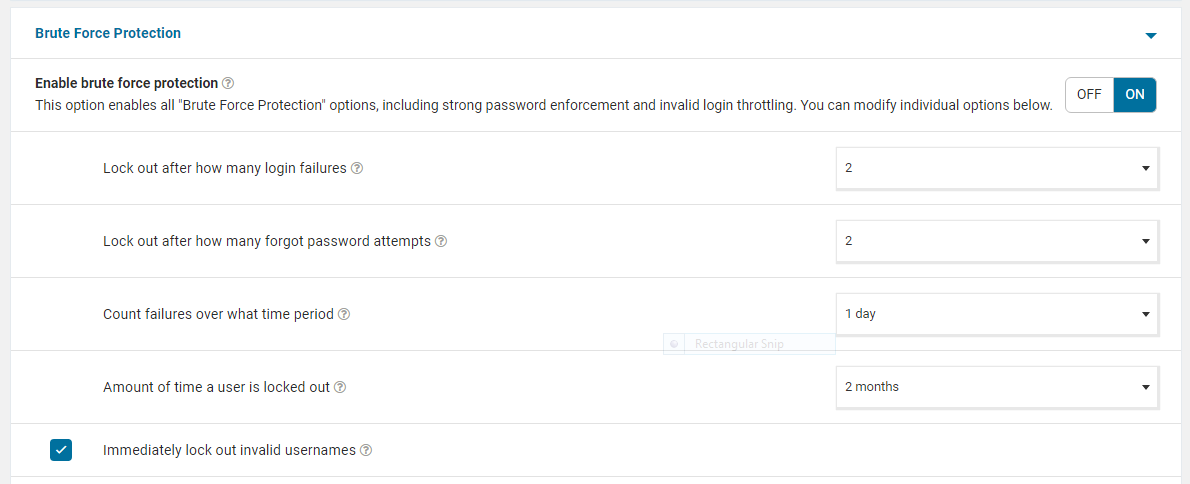
- Brute Force Protection:
- Lockout after 2 failed login attempts
- Lockout after 2 password forgotten attempts
- Period within which failures are counted: 1 day
- Period within which the user remains in lockout: 2 months
- Automatically block incorrect username: active
- Prevent passwords from being leaked in data breaches: For all users
- (Optional) Limit the ‘Maximum e-mail alerts to send per hour’ in the ‘E-mail Alert Preferences’ to 5 per hour or less. This way you will avoid that the mail functions of your e-mail are blocked because there are too many e-mails being sent as alerts.
Best practises for optimal WordPress security
Of course, a security plugin is not enough. Within WordPress itself there are a number of best practices that you should follow:
- Don’t use generic usernames. Usernames such as “admin”, “administrator”, or “webmaster” are not secure. These are the first usernames hackers will try during a brute force attack. Is your name somewhere on the website? Avoid using it as a login. In this way, hackers will try that one as well.
- Go easy on the admin rights. Do not just give every user an administrator account. In fact, limit it to the minimum permissions. Have in mind, a user with Editor rights will already have enough to change your content.
- Enable two-factor authentication. Provide (where possible) 2-factor authentication for every user.
- Keep everything up-to-date. WordPress is a very popular platform, which means that there is both a huge developer community behind it (which helps to resolve issues and leaks faster through updates), and that WordPress gets more attention from hackers (which means leaks can be exploited more quickly). That is why it is important to respond quickly to updates. I would recommend checking for updates daily or at least every other day, and install the updates as soon as they become available.
- Delete plugins that do not get updated (anymore). Also check if the plugins you are using are still being maintained. Sometimes plugins are “abandoned”, which means that the plugin is still available in the repository, but the developer is no longer working on it. You can check this on the plugin page on WordPress.org.
For example: https://wordpress.org/plugins/akismet/
On the right side of the page you can see when it was last updated. It is probably not a good idea to use a plugin that has not been updated for the last 12 months. If you use a management tool like MainWP, it will also bring to your attention plugins that are no longer maintained (and thus become a potential risk).
Secure your server via .htaccess
In addition to working with your WordPress to protect it, you can also provide some necessary security at server level.
You can restrict access to certain files via the .htaccess file. You can find some concrete examples of this on Brecht’s blog: https://brechtryckaert.com/wordpress/improving-wordpress-security-with-the-htaccess/. Of course, this is the absolute basics, but you can still secure more files and directories via the .htaccess, based on the specifics of your website.
We hope this article was helpful. To complete the efforts you are paying to protect your WordPress, never forget to always follow the general rules to prevent your website from getting hacked.